SpartaNews

My way in cybersecurity
16th Nov 2021
A woman who works in a male-dominated field cannot usually say it’s easy. It has its advantages and disadvantages.When I started my professional career, I did not know what it would look like. I’ve always believed that doing complicated things like analyzing information to keep it safe or the security of data, people, computers, devices, networks was difficult. When I was offered a job at NASK, I had divergent thoughts about it. I felt it could be a big challenge, maybe even too big? I was ...
More >>
High Assurance Intelligent Infrastructure Toolkit: Program Results
21st Oct 2021
Program goalsThe High Assurance Intelligent Infrastructure Toolkit (HAII-T) Program deals with the menaces to the security of the modern, smart infrastructures. Intelligent infrastructures are objects of extreme complexity (aka systems of systems) which are difficult to protect and, contemporary, very appealing for an attacker.
The cornerstone of the HAII-T Program is that security must be considered along the entire life cycle of an infrastructure, starting from the very initial design fa...
More >>


Secure and fair AI systems for citizens: Program Results
21st Oct 2021
The expansion of artificial intelligence (AI) has opened the doors for advancements and improvements in almost every domain of human life. However, the development of AI comes at a cost – the methods are not bulletproof, and may be thwarted by a number of issues, among them two major ones. One regards the technical side of it and is related to the fact how many new cyberattacks keep emerging, and consequently, require employing adequate countermeasures. The other set of challenges to the succ...More >>
SPARTA | The Future Needs You
18th Oct 2021
The instant interconnectivity brought by the rapid advances in technology revolutionised the way we lived and changed the paradigm of security. Cyberspace is a place shared by all the citizens, where social, political, and economic aspects are constantly emerging. As in the physical world, cyberspace faces a range of emerging challenges, namely concerning its security.An interconnected world means that cyberattacks can come from any part of the world. Cybercriminals, or non-ethical hackers,...
More >>


Local explanation of Machine Learning model with shapkit, a Python module that approximate Shapley Values
4th Oct 2021
Nowadays, Machine Learning models are used for various applications with already successful or promising results. Unfortunately, a common criticism is the lack of transparency associated with these algorithm decisions. This is mainly due to a greater interest in performance (measurable on specific tasks) at the expense of a complete understanding of the model. This results in a lack of knowledge of the internal working of the algorithm by the developer and the end user. The most obvious conse...More >>
National Clusters pushing the JCCI growth
27th Sep 2021
European Commission has funded four different pilots for establishing a European Cybersecurity Competence centre, promoting share competences, expertise and knowledge among the institutions, stakeholders, and other members. In this context, in SPARTA project, the Joint Competence Centre Infrastructure is implemented as a solution for addressing these Commission’s needs.The mission of a Joint Competence Centre Infrastructure is to promote and make available information about tools, infrastru...
More >>

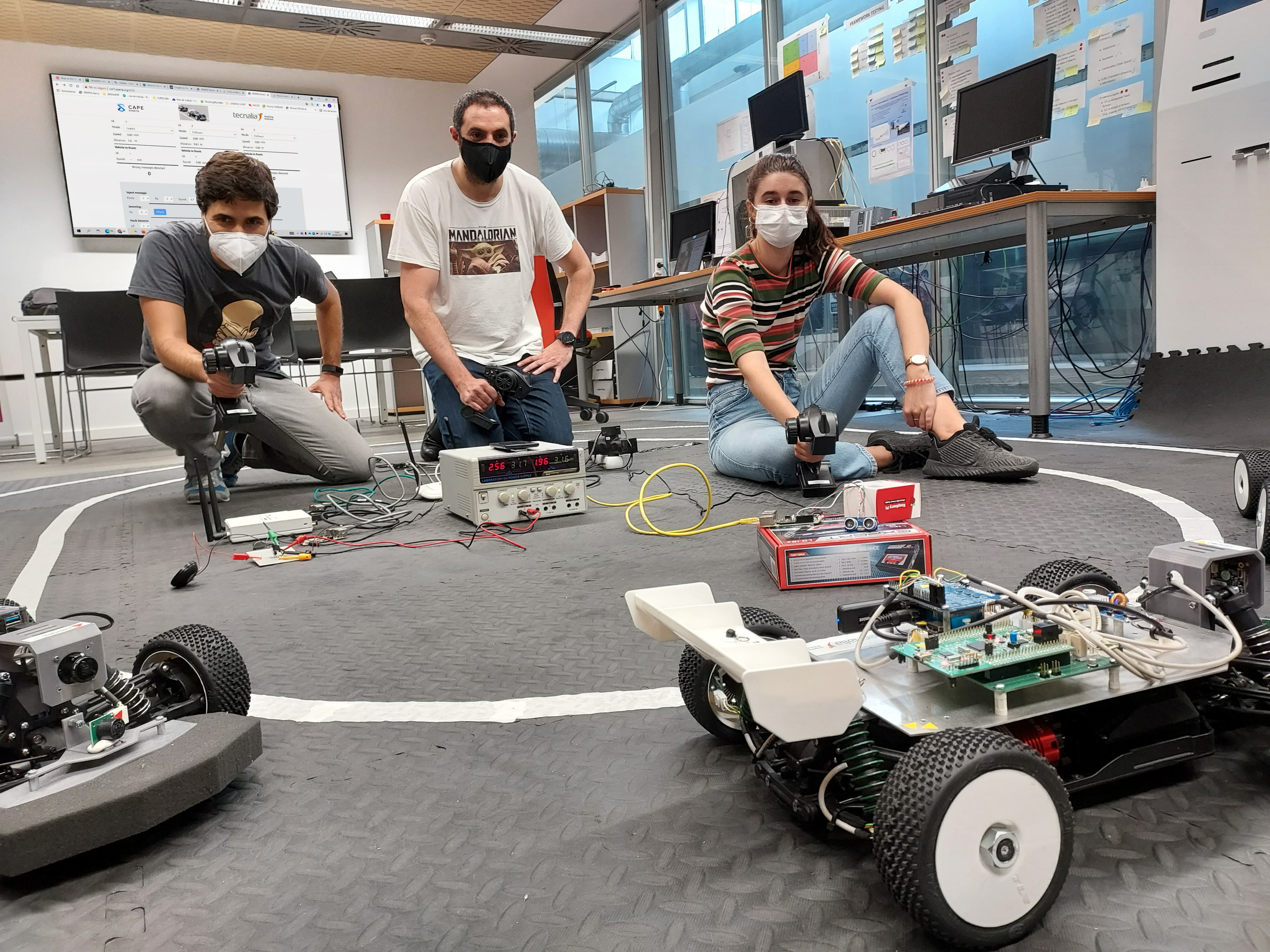
Evaluation of the Cooperative Car demonstrator developed by TECNALIA in the CAPE program
17th Sep 2021
Last week EURECAT technology centre has visited the TECNALIA’s Autonomous Vehicle Cybersecurity laboratory, which is one of the laboratories that forms the BDIH Cybersecurity Node. The aim of the visit was to carry out, together with the TECNALIA team, a penetration test on a fleet of Model Cars while they circulate jointly and in a coordinated manner forming a platoon. This work is part of SPARTA!In SPARTA, TECNALIA is working on the assessment and improvement of the security of connected ...
More >>
Turris OS 5.2 has bee released
8th Sep 2021
About Turris project:Project Turris started back in 2013. It was a security project sponsored by CZ.NIC to get more relevant data about attacks on average Joe. As part of the project, routers with custom software were created and given away to Czech Republic households. Those routers were under contract, which stated that they had to be the main access point to the Internet. From those routers, firewall logs were collected. Apart from firewall logs, some minimalistic honeypots were written ...
More >>

SPARTA at the 47th edition of the Cybersecurity Breakfast
2nd Sep 2021
AGENDAThe 47th edition of the Cybersecurity Breakfast was organized in cooperation with the SPARTA project. It was focused on lessons learned while effectively transforming cybersecurity research into innovation.
The agenda was divided in 3 parts:
A keynote by Dr Mart Noorma, Science and Development Director at Milrem Robotics, Professor of Space and Defense Technology at University of Tartu (Estonia), on “Lessons learned from a highly innovative company, working for years with both ac...
More >>
Personal Data Breach Regulation
27th Jul 2021
Article 33 of the General Data Protection Regulation 2016/679 (GDPR) requires that, as soon as the data controller becomes aware that a personal data breach has occurred, it should without undue delay and, where feasible, not later than 72 hours after having become aware of it, notify the personal data breach to the supervisory authority, unless the controller can demonstrate that the breach is unlikely to result in a risk for the rights and freedoms of individuals. “Personal data breach” is ...More >>
